Introduction to Computer Science: The Basics (Part Two Final)
Part two of an introduction to computer science
Feedback
User
The quality and success of a program relies on the opinions and experiences of its users.
User-centered design is an approach to program development that places the wants and needs of users. It involves considering users' perspectives, preferences, and requirements throughout the entire design process to ensure the program is efficient and valuable. When creating a user-centered design you should focus on:
Usability: How easy it is to use
Accessibility: Can people with disabilities use it
Content: Does it fit with your target audience
Before releasing a program to the public, programmers often engage in alpha and beta testing to gather valuable feedback from users.
Alpha testing involves testing the program internally, typically within the development team or a select group of individuals, to identify and address any issues or bugs.
Beta testing involves external users (outside the development team) who are willing to provide feedback. These users interact with the program, explore its features, and report any bugs they encounter.
Sharing your program with users before its official release will help identify flaws that may have been overlooked. By seeking feedback and fixing the issues, your program will be more reliable, and user-friendly when it goes out into the world.
Collaborating
Working with others on programming projects is useful as it can help finish the project faster and reduce the burden on the programmer.
Google Chrome runs on 6.7 million lines of code and the Android operating system runs on 12-15 million lines. Writing a million lines of code by yourself would take a long time. That is why collaborating on a project will help you build more efficient programs more quickly.
Some collaboration tips:
Setting clear expectations
Assign tasks to a person’s strength
Have realistic timelines
Give out equal workloads
Have clear roles
Libraries
Libraries are useful resources that provide a collection of pre-made functions and tools to assist programmers in their development tasks. They allow developers to leverage existing code that is pre-made to serve a specific function. Without it, developers would have to type hundreds of code from scratch.
Algorithms
Algorithms play an important role in both human and computer processes, as they provide a set of instructions or steps that can be followed to accomplish a specific task. It’s basically a recipe.
Algorithms play a fundamental role in providing clear instructions for carrying out repetitive tasks. Different algorithms can be used to solve the same task. It provides the opportunity to choose the most suitable one based on specific requirements.
Developing algorithms is a distinct field within computer science that is similar to the study of mathematics.
Computer scientists are tasked with solving problems by coming up with solutions, transforming those solutions into algorithms, and then implementing the algorithms as computer programs. A program is the implementation of an algorithm in the form of executable code. Algorithms are written in a way we understand.
Programmers would give instructions to the computer by using programming languages. They’re a combination of words, symbols, numbers, and formatting to tell a computer what to do.
History of Programming
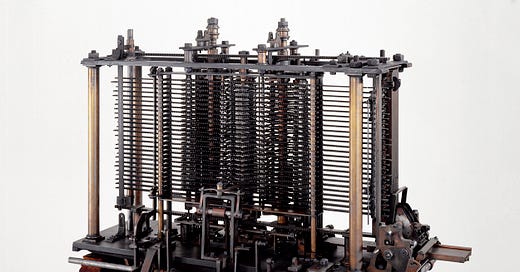
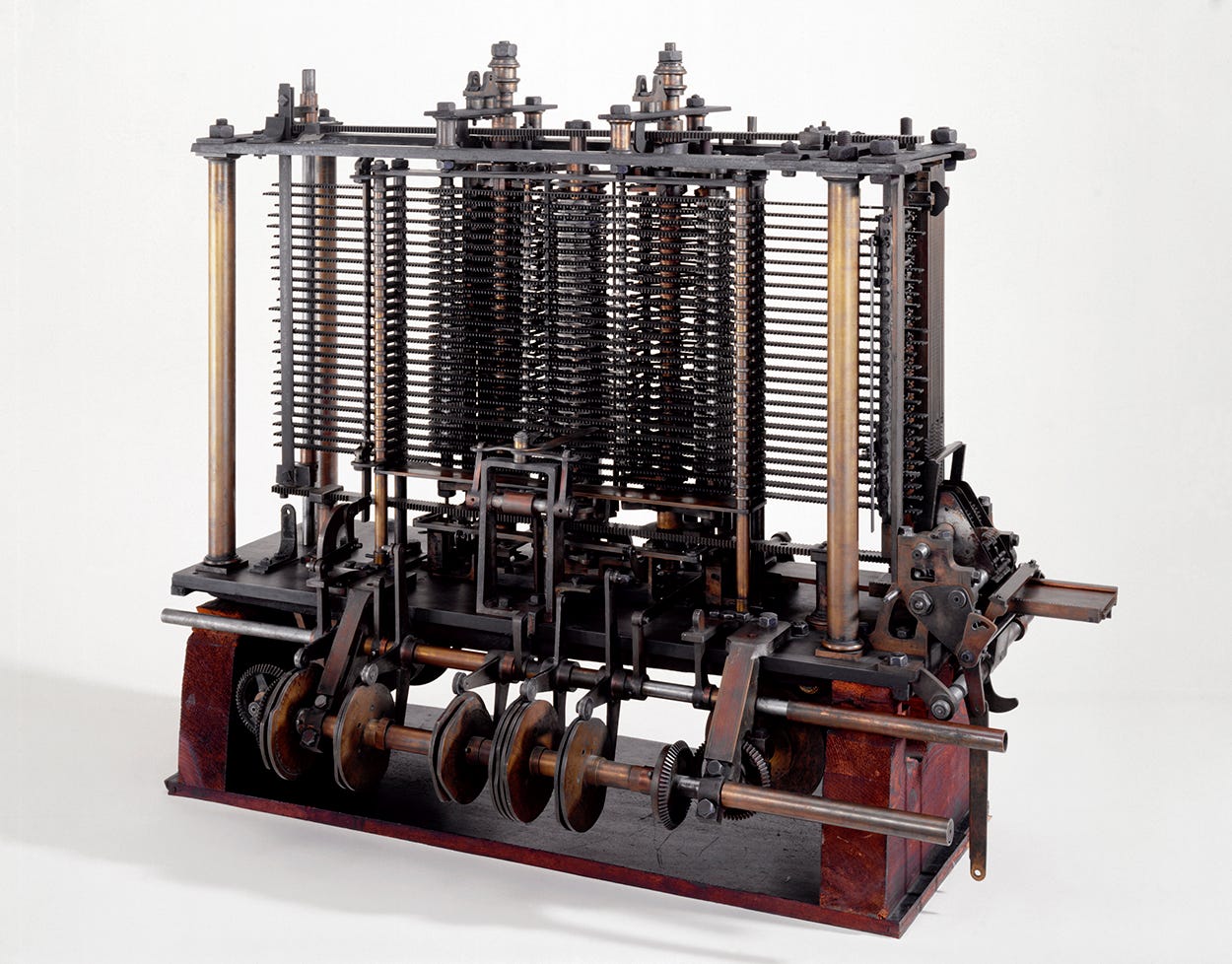
Ada Lovelace is recognized as one of the first programmers due to her work on the analytical engine, a mechanical computer designed by Charles Babbage.
The analytical engine was operated using punch cards. These punch cards contained holes that represented specific instructions for the machine to process. By feeding the punch cards into the machine, users could program the analytical engine to perform specific calculations or tasks.
Programming Languages
There are hundreds of programming languages programmers use for different types of tasks. Languages such as Python, PHP, and Javascript are used to make web pages. A collection of them is called websites.
Mobile applications (designed to run on cell phones and tablets) used other programming languages such as Java, Kotlin, Swift, and more.
Each programming language has its own strength and weakness. Some might be faster than others, some might be easier to write, and some show graphics better. Programmers may use more than one language for a large project.
Javascript is considered a front-end language, which is mainly used to make part of a website. A front-end language is specifically designed for creating the visible and interactive elements of a website that users see and interact with on their screens. It focuses on the user interface and user experience aspects of web development such as the layout, typography, colors, images, and other elements.
If we want to store a lot of information then we need a different type of programming language specifically a back-end type. The back-end of a website or application is responsible for handling data storage, processing, and management. It focuses on tasks such as handling user authentication, managing data storage and retrieval, and integrating with external systems or APIs.
Binary
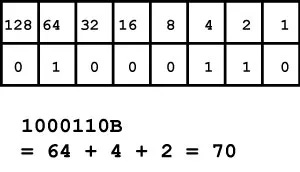
Computers rely on electrical circuits to process information, and the circuits can be in either an ‘on’ or ‘off’ state. Computer scientists use the binary system, which represents ‘on’ as 1 and ‘off’ as 0. This binary encoding, also known as machine code, allows computers to understand and manipulate data. In binary, each digit is referred to as a bit, and it can only have two possible values: 0 or 1.
The CPU is designed to execute instructions written in machine code. However, we typically write programs in programming languages since they’re easier to understand and work with. In order for the CPU to execute these programs, they need to be translated into machine code. This process is called compiling. A compiler is a software program that takes the ‘human’ code and converts it into machine code that the CPU can execute.
Before the compiler was invented, programmers have to write programs in a language similar to machine code.
Binary is a numerical system that uses only two digits, 0 and 1, to represent numbers and perform counting operations. Unlike our decimal system that uses 10 digits (0-9), binary operates on a base-2 system, where each digit's value is determined by its position in the number.
Basically, if you’re trying to find a number such as 93:
Here is another example:
Letters in Binary
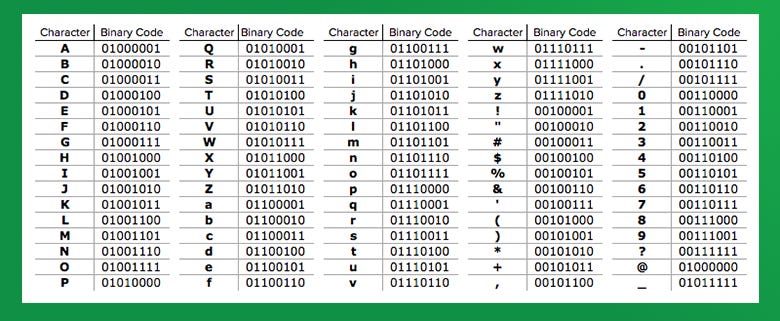
The American Standard Code for Information Interchange (ASCII) has assigned each letter of the alphabet and symbols to a specific number.
For example, the capital letter B is assigned to the number 66, which in binary is 01000010. A program will tell the computer if it should interpret it as numbers or letters.
But here is the full alphabet in binary code:
Bytes and Bits
A bit is the smallest unit that represents one digit (0 or 1).
The next measurement is a byte which represents 8 bits.
The maximum number that can be represented with 1 byte is 255 or 11111111. This is why RGB runs from 0 to 255.
When dealing with large quantities of bytes, we often use prefixes to represent them in a more understandable way. These are:
Kilobyte (KB): around one thousand bytes
Megabyte (MB): around one million bytes
Gigabyte (GB): around one billion bytes
Terabyte (TB): around one trillion bytes
Creating algorithms
Before writing code for a program, programmers typically create an algorithm. To plan and design algorithms effectively, they often use tools like pseudocode and flowcharts.
Pseudocode is written in an informal language for programmers to understand. It is meant for us to understand, not computers. It helps programmers outline the logic and structure of their code.
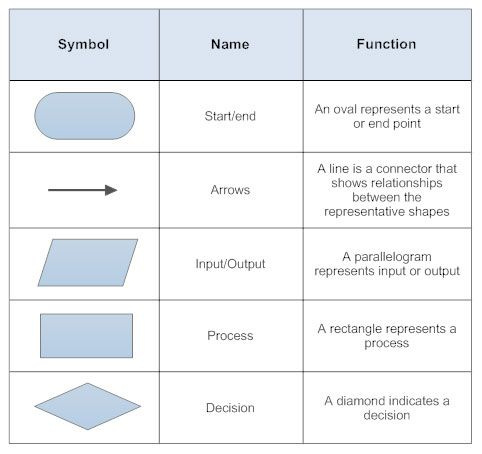
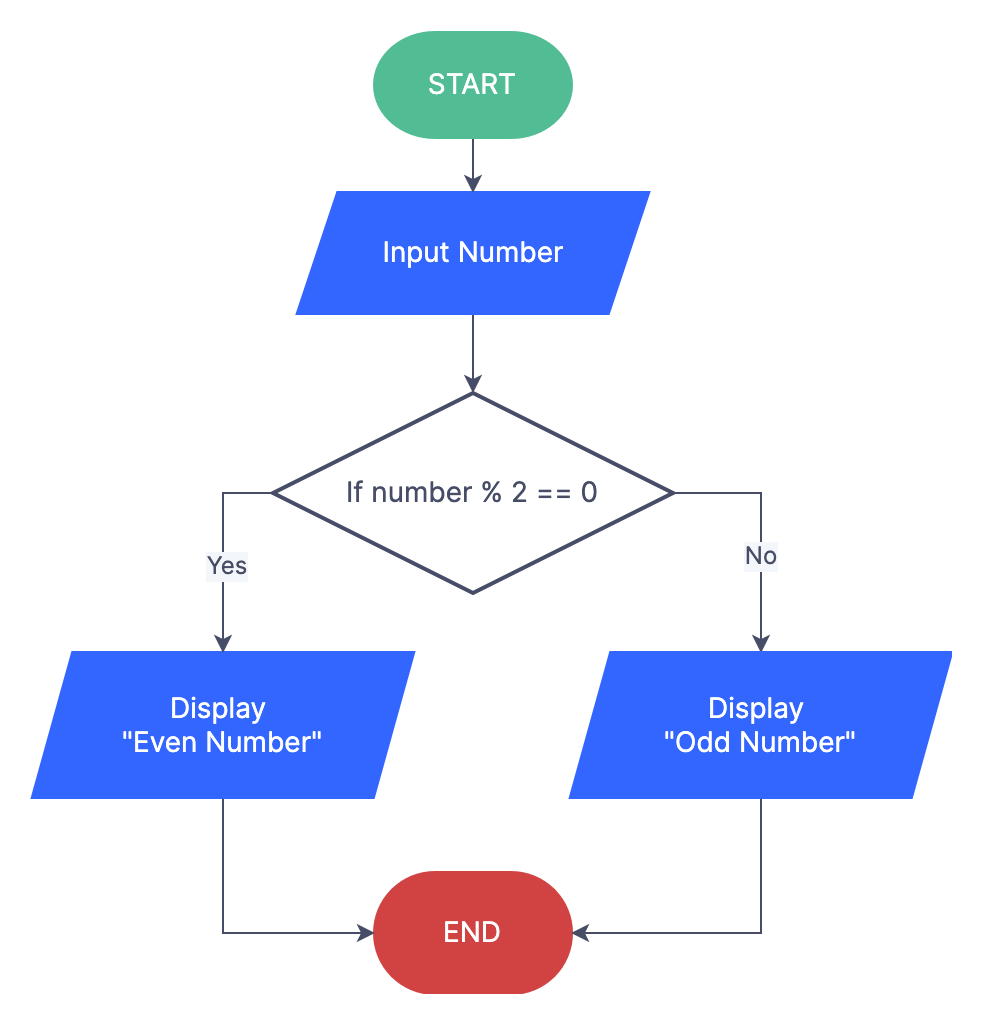
Flowcharts use visual symbols and arrows to represent the flow of control and decision points within an algorithm. They use specific symbols that represent different parts:
Here is an example:
Computational Thinking
Computational thinking is the thinking process of creating solutions that can be executed by computers.
There are four ideas in computational thinking:
Decomposition: Breaking down the problem into smaller easier parts
Abstraction: Dividing important details from less important details
Pattern Recognition: Identifying patterns in the data set
Algorithm Design: Creating solutions to the problem
Decomposition
Before tackling a problem, it's crucial to have a comprehensive understanding of all the parts of the problem. After that, you can break the problem into smaller, more manageable tasks. This would simplify the problem as you’re now focusing on smaller easier pieces rather than the whole problem.
Abstraction
Abstraction is focusing on the most important details of a problem and just leaving the unimportant details alone
Pattern Recognition
Patterns are recurring events and when solving problems, recognizing patterns becomes useful as it allows you to leverage previous solutions to tackle new problems more effectively. By identifying similarities between current and past problems, you can use existing solutions and adapt them to complete different tasks.
Algorithm Design
Algorithms design is writing out instructions that need to be followed to achieve a specific outcome consistently. The benefit of algorithm design is that once you have a well-defined algorithm, you can apply it repeatedly to obtain the same solution each time.
Programming Principles
Variable
Variables serve as containers for storing and manipulating data during program execution. They are allocated memory space to hold values, which can be accessed, modified, and utilized throughout the program.
Variables have names, known as identifiers, which allow us to refer to and manipulate their stored information. The value of a variable represents the data it holds such as text, numbers, or other data formats. The identifier serves as a unique label for the variable which allows us to work with its associated value throughout the program.
To create a variable you have to declare it. This will allow the computer to create space for the information and assign it. You would use the equal sign (=) to assign a value to a variable. Identifier is on the left and the value is on the right.
There are different rules for identifying or naming variables in different programming languages.
Information Variables Store
Variables can store different kinds of information such as:
String Values: Store any kind of character (numbers, symbols, letters). It is placed inside quotation marks.
Numeric Values: Store integers (whole numbers negative or positive) or floating point numbers (decimals). You would not use quotation marks for this. You can use algebraic expressions when assigning values.
Boolean Values: They can only have two values: true or false.
Lists: An array variable that lets you store multiple pieces of information in one place.
Conditional Statements
Conditional Statements only run when a certain condition is met. It is basically the if…then statement. For example:
If it’s raining, then I will wear a raincoat
If it snows, then I build a snowman
You can have a different action if the condition is false. You would use an else statement. For example:
If it’s raining, then I will wear a raincoat
Else I will wear my normal clothes
If it snows, then I build a snowman
Else I will take a walk
You can also have multiple conditional statements. You would use else if in an ‘if’ statement (the syntax may be different in various programming languages, but it will follow the same logic). This would add another action.
Comparison Operators
They are used in logical statements to determine whether two values are equal, not equal, greater than, less than, or other similar comparisons.
Compound Conditionals
Compound conditionals are used to combine multiple boolean expressions into a single logical statement.
Logical operators are used to combine boolean expressions. The three most common logical operators are ‘AND,’ ‘OR,’ and ‘NOT.’
AND statements are true when both conditions are true. If one of them is false then the statement is false
OR statements are true when one of the conditions is true. If both are false then the statement is false
NOT statements reverse the value from false to true and true to false. So NOT false would be true and NOT true would be false.
Nested Conditional
A nested conditional is where one conditional statement is placed within another conditional statement. They are commonly used in situations where multiple levels of conditions need to be evaluated to determine the course of action.
Loops
Loop statements provide a way to repeat a specific block of code multiple times. By using loops, you can avoid writing the same code over and over again.
There are different kinds of loops:
For loop executes a block of code a specified number of times
While loop will repeat as long as a given condition remains true
Nested loop is where one loop is placed inside another loop. This allows for the repetition of a block of code within another block of code.
Events
Events are triggers that initiate specific actions or behaviors within a program. They can be user interactions, such as clicking a button or pressing a key, or system events like a timer reaching a certain interval.
An event handler is a block of code that is executed when a specific event occurs. It is responsible for defining the actions that should be performed in response to the event. When an event is triggered, the associated event handler is invoked to handle the event and perform the desired tasks.
Procedures
A procedure is a reusable block of code that performs a specific task or set of tasks. It allows you to encapsulate a series of instructions into a single unit that can be called or invoked whenever needed. It is a great way to organize the code.
In order to create a procedure, you have to declare it by giving it a name and the code that you want to use as a procedure. After that when you’re ready to use the code, you have to call it. It can be called multiple times as you want.
Parameters are variables that are defined within a procedure and receive values from the code that calls the procedure.
The Web
Networks
A network is a collection of computers that are interconnected, allowing them to communicate and share information with one another.
A local area network (LAN) is a network that connects computers and devices in a limited geographical area, such as a home, office, or school campus.
Computers communicate through the use of ethernet (wires) or wireless (no wires).
Internet
The Internet is a global network that connects millions of computers and networks worldwide. The Internet enables the transmission of data, communication, and access to a wide range of resources and services. It allows users to browse websites, send emails, stream videos, and a lot more.
The History of the Web
Tim Berners-Lee was known as the inventor of the World Wide Web. He created:
The first web browser, WorldWideWeb
Hypertext Markup Language (HTML) is used to structure website
Hypertext transfer protocol (HTTP) is used to send information over the web.
Sending Information
When downloading files from the internet, large files are divided into smaller units called packets. These packets contain portions of the file's data and are sent individually over the network. Each packet carries information about its destination, source, and position within the file. Once the packets reach your device, they’re reassembled in the correct order to reconstruct the complete file.
An IP address serves as a unique identifier for devices connected to a network. It is used to ensure that packets are directed to the correct destination. Each device connected to a network is assigned a distinct IP address.
Where a Website Lives
Each website has a uniform resource locator (URL). When you type in a URL, your computer will first ask the domain name system (DNS) server for the IP address of the server that is hosting your site. Your computer then uses that IP address to find the correct server and then asks the server for the HTML files used to make a website. After that, the server follows a transmission control protocol (TCP). A TCP is a set of rules computer use when transferring information.
Another way is to use a user datagram protocol (UDP) to transfer information. This is mainly used for speed but is less reliable than TCP.
Cybersecurity
Cybersecurity is needed to keep information safe. Here are some techniques:
Authentication: used to confirm someone’s identity before giving access to information. This may include username and password, face recognition, and fingerprint.
Two-factor authentication: combines two different types of authentication
Access Control: allows authorized users to have access to specific information.
Sandboxing: isolates applications within a secure environment, restricting their access to the rest of the computer system.
Cryptography: scramble information so no one except authorized people can unscramble and read them. This process is known as encryption and decryption. Encryption is when the information is transformed into a secret message and decryption is turning the secret message into readable information.
Hackers
People who break into computers. There are many different kinds of hackers such as:
Black hat hackers who steal information
White hat hackers who hunt for bugs and fix them
Hacktivists who break into the system to achieve a political goal
Attacks
Hackers use a wide array of attacks to break into systems such as:
Brute force: uses the computer to guess every authentication
Malware: harmful software installed on a computer such as ransomware, spyware, trojan, virus, or worms
Social engineering: pretending to be someone else like a company or person. Phishing is one type of social engineering where attackers pretend to have legitimate websites or emails
Distributed denial-of-service (DDoS): hackers use lots of computers to send a lot of messages to a server causing it to crash
[End]